How to Protect Your Crypto Wallet from Hacking and Theft

In a rapidly evolving financial landscape, cryptocurrencies are more than just an investment—they are a gateway to a world full of opportunities and challenges. Whether you are a beginner looking to grasp the fundamentals of trading or a professional trader keeping up with the latest developments, this article provides everything you need to stay informed and make smart financial decisions. We will explore the latest news, secure trading strategies, market analysis, and emerging global trends to keep you ahead in the world of trading.
Key insights you\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\’ll gain from this guide
- Cryptocurrency news and developments: Stay updated with the most important happenings in the crypto market.
- Safe trading techniques: Tips to protect your assets and reduce trading risks.
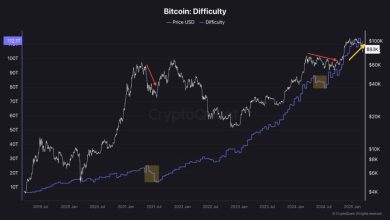
- Market analysis: Expert insights into price trends and market behavior.
- Global trends and innovations: Understand the emerging directions shaping the crypto world.
As cryptocurrencies continue to gain global popularity, the importance of securing digital assets has never been greater. Unlike traditional banking systems, where institutions can reverse fraudulent transactions or recover stolen funds, cryptocurrency transactions are irreversible.
This makes crypto wallets a prime target for hackers and cybercriminals.Whether you are a beginner or an experienced investor, understanding how to protect your crypto wallet is essential. In this article, we explore the most effective strategies and best practices to safeguard your digital assets from hacking and theft.
Understanding Crypto Wallets
Before diving into security measures, it’s important to understand what a crypto wallet is. A cryptocurrency wallet is a digital tool that allows users to store, send, and receive cryptocurrencies. Wallets do not actually store coins but rather the private keys that grant access to your funds on the blockchain.
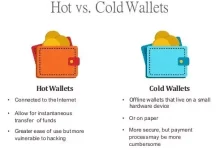
There are two main types of wallets:
- Hot Wallets: Connected to the internet (e.g., mobile apps, web wallets)
- Cold Wallets: Offline storage (e.g., hardware wallets, paper wallets)
Hot wallets are more convenient but more vulnerable to cyberattacks, while cold wallets offer higher security but less accessibility.
1. Use Strong and Unique Passwords
One of the simplest yet most effective ways to protect your crypto wallet is by using a strong, unique password. Avoid using common phrases, personal information, or passwords you’ve used elsewhere.
A strong password should:
- Be by least 12–16 characters long
- Include uppercase and lowercase letters
- Contain numbers and special characters
Additionally, never reuse your wallet password on other platforms. If one account is compromised, reused passwords can expose your crypto wallet to attackers.
2. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security by requiring a second verification step in addition to your password. This is typically a code generated by an app or sent to your device.
Using 2FA significantly reduces the risk of unauthorized access, even if your password is compromised. It is recommended to use authentication apps rather than SMS-based codes, as SIM-swapping attacks can bypass SMS verification.
3. Store Your Private Keys Securely
Your private key is the most critical component of your crypto wallet. Anyone who has access to your private key can control your funds.
Top practices include:
- Never share your private key with anyone
- Do not store it in plain text on your computer or phone
- Write it down and store it in a secure, offline location
Consider using hardware wallets to store private keys offline, making them inaccessible to online hackers.
4. Use Hardware Wallets for Large Holdings
If you hold a significant amount of cryptocurrency, using a hardware wallet is one of the safest options. Hardware wallets store your private keys offline, making them immune to most online attacks such as phishing, malware, and hacking attempts.
These devices require physical confirmation for transactions, adding another layer of protection.
5. Beware of Phishing Attacks
Phishing is one of the most common methods used by hackers to steal crypto assets. Attackers often create fake websites, emails, or messages that mimic legitimate platforms.
To avoid phishing:
- Always check the website URL carefully
- Avoid clicking on suspicious links
- Do not download attachments from unknown sources
- Bookmark official websites and use them directly
Even experienced users can fall victim to sophisticated phishing scams, so vigilance is key.
6. Keep Your Software Updated
Outdated software can contain vulnerabilities that hackers exploit. Ensure that your wallet app, operating system, and antivirus software are always up to date.
Regular updates often include security patches that protect against newly discovered threats. Ignoring updates can leave your wallet exposed to avoidable risks.
7. Avoid Public Wi-Fi Networks
Public Wi-Fi networks are often unsecured and can be exploited by hackers to intercept your data. Accessing your crypto wallet on public networks increases the risk of being targeted by cybercriminals.
If you must use public Wi-Fi, consider using a Virtual Private Network (VPN) to encrypt your internet connection and protect your data.
8. Use Multi-Signature Wallets
Multi-signature (multi-sig) wallets require multiple approvals before a transaction can be executed. This adds an additional layer of security, as a single compromised key is not enough to access funds.
Multi-sig wallets are especially useful for businesses or individuals managing large amounts of cryptocurrency.
9. Backup Your Wallet Regularly
Backing up your wallet ensures that you can recover your funds in case of device loss, failure, or theft.
Important backup tips:
- Store backups in multiple secure locations
- Use encrypted storage devices
- Keep backups offline whenever possible
Without a proper backup, losing access to your wallet could mean permanently losing your funds.
10. Be Cautious with Third-Party Apps
Many third-party apps and services offer crypto-related features, but not all of them are trustworthy. Some may contain malicious code designed to steal your private keys or sensitive data.
Only use reputable and well-reviewed applications. Always verify the authenticity of the app before downloading or connecting it to your wallet.
11. Monitor Your Transactions Regularly
Keeping track of your wallet activity can help you detect suspicious transactions early. If you notice any unauthorized activity, take immediate action by transferring your funds to a secure wallet.
Early detection can minimize losses and prevent further unauthorized access.
12. Educate Yourself Continuously
The crypto space evolves rapidly, and so do hacking techniques. Staying informed about the latest security threats and best practices is essential.
Follow trusted sources, join crypto communities, and keep learning about new ways to protect your assets.
Common Mistakes to Avoid
Even experienced users sometimes make critical mistakes that lead to loss of funds. Avoid the following:
- Sharing private keys or recovery phrases
- Falling for “too good to be true” investment offers
- Ignoring security updates
- Storing large funds in hot wallets
Awareness of these mistakes can significantly reduce your risk.
The Human Factor in Security
It is important to recognize that most crypto thefts are not due to advanced hacking techniques but rather human error. Social engineering attacks, phishing, and poor security habits are often the weakest links.
By adopting disciplined security practices, users can greatly reduce their exposure to risk.






Very helpful breakdown of altcoin performance.
I love the detailed explanations of market events.
Great explanation of how blockchain technology actually works.